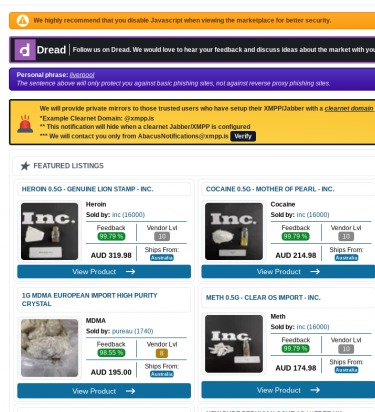
Clicking the wrong link from a dark web search engine can trigger malware infections, data theft, or access to ransomware. While this makes it dangerous for most, its completely open nature allows cybersecurity researchers to access a wider, unfiltered range of dark websites. The dark web operates on encrypted networks and uses protocols that traditional search engines can't access.
- That’s right — people widely use this popular privacy search engine on Tor.
- The search engine itself might be safe, but the links it gives you might not be.
- Scammers create cloned onion addresses that appear legitimate in search results.
- Tor Search constantly crawls (onion) websites 24 hours a day, 7 days a week.
- It might show you directories or references to them, but for serious dark web exploration you’ll need other engines on this list.
PGP verification, security ratings, and detailed warnings for each listed service Plus, it’s slower since your data travels through the same four steps – entry node, relay node, exit node, and then the VPN server. By connecting to a VPN before using Tor, you mask your real IP address before it reaches this entry node, adding an extra layer of security and anonymity.
Only the exit node sees the final destination of the data, but it does not know the original source. There are three primary types of nodes in the Tor network. Data sent over the network typically passes through several randomly selected relays before reaching its final destination. The Tor network consists of thousands of volunteer-run relays around the world. The third level is the safest and JavaScript is off on all sites and fonts are disabled. The second level is safer and JavaScript is disabled on non-HTTPs sites and audio and video elements don't auto-play.
In today’s digital age, the internet offers a vast array of resources, but not all of them are easily accessible through traditional search engines. One of the most intriguing aspects of the web is the .onion links, which are part of the Tor network. These links provide users with a unique browsing experience that emphasizes privacy and anonymity. Understanding how .onion links work can empower individuals to navigate the internet more securely and responsibly.
Onion Links
.onion links are a special type of web address that can only be accessed using the Tor browser. The Tor network was developed to enhance privacy for users, allowing them to browse the internet without being tracked. As a result, .onion sites make up a significant part of what is often referred to as the "dark web." However, it's essential to note that .onion links aren't necessarily associated with illegal activities; many of them serve legitimate purposes, including political activism and providing information in oppressive regimes.
How Do .Onion Links Work?
- I have considered many options for a secure way to access .onion sites, but I have not been able to find one.
- Now Riseup has grown to over six million users worldwide.
- And because they aren’t searchable via Google or Bing, onion site lists are important roadmaps to help users find what they’re looking for on the dark web.
- Unlike the surface web, where search engines like Google or Bing catalog and index sites for easy access, the Dark Web operates on a different set of principles.
- Of course, we can argue whether tor is better than a good VPN til we’re blue in the face, but it would be great for those just starting to experiment to have a safe DW site to visit.
- All you need to do is click connect and you are officially connected to the Tor network and can now access dark web websites.
The core of the Tor network is its ability to route your internet connection through multiple servers, which masks your IP address and encrypts your data. When you access a .onion link, your browser connects to a hidden server that is also on the Tor network. This connection is specifically designed to be private and secure, making it difficult for third parties to monitor your online activities.
Accessing .Onion Links
To visit .onion links, you must first download and install the Tor browser. This specialized browser is designed to interface with the Tor network seamlessly. Once installed, you can enter .onion addresses directly into the browser's address bar. Keep in mind that these links often change frequently and may not be indexed in traditional search engines, making them challenging to discover without prior knowledge or specific guides.
Common Uses of .Onion Links
While the idea of .onion links may conjure images of illicit activities, many sites serve crucial functions. Some common uses include:
- Whistleblowing Platforms: Sites like SecureDrop allow whistleblowers to share sensitive information with journalists while maintaining anonymity.
- Forums and Communities: Certain online communities discuss topics that may be sensitive or restricted in certain regions, promoting free speech and information sharing.
- Privacy-Focused Services: Various services offer privacy-oriented products and communications tools that protect user data.
Risks and Considerations
While accessing .onion links can provide anonymity and privacy, it is not without risks. Users should be cautious of malicious sites that may attempt to exploit vulnerabilities or gather personal information. Moreover, understanding the legal implications of browsing certain .onion sites is crucial; engaging in illegal activities can lead to serious consequences.
Conclusion
Understanding .onion links is essential in the context of today’s digital landscape. By using the Tor network responsibly, individuals can explore the internet with a reinforced sense of privacy and security. However, awareness of both the benefits and risks associated with these links is vital for informed internet usage. The Tor network has opened doors to information flow that might otherwise be stifled, empowering users to access valuable resources responsibly.