The UI also showed when the victim’s device was infected by the malware and when it was last updated, and Genesis provided customers with a wiki on how to abuse victims’ credentials. The UI showed how many logins and what accounts each bot contained; the more logins provided, the more expensive the bot, especially when it included bank or crypto account credentials. The information-stealing malware package that Genesis Market used to exploit victims included a hidden Chromium-based browser plugin, made to look like a Google Drive plugin, which captured credentials stored in victims’ browsers. In order to gain control of victims’ computers, the malware Genesis Market employed used a legacy Bitcoin address to determine the command-and-control (C2) server, from which cybercriminals initiated remote access to infected devices.
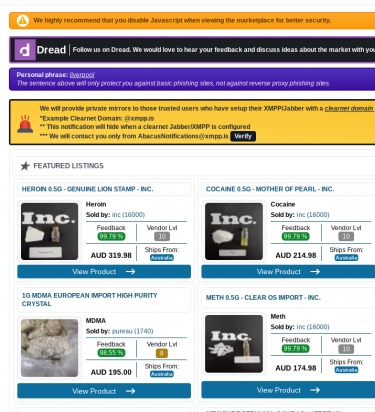
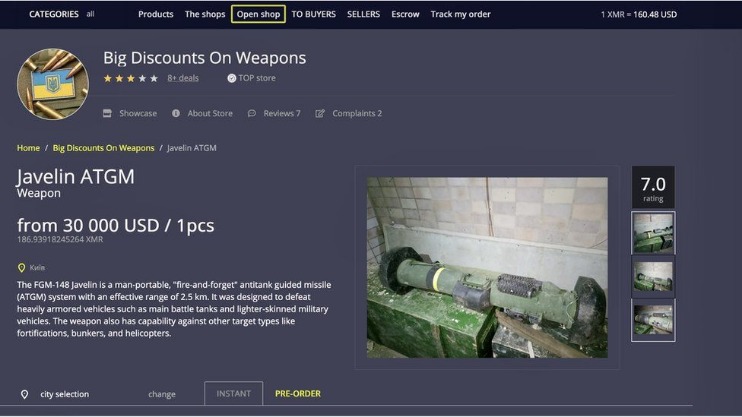
Dark web and darknet markets are where stolen credentials get monetized. This expansion means security teams need to monitor beyond just Tor-based marketplaces. Some vendors operate exclusively on Telegram, bypassing traditional darknet markets entirely.
The increasing interest in digital privacy and cybersecurity has brought various tools and resources into the limelight, one of which is the abacus darknet url. As the digital landscape evolves, understanding these resources becomes critical, particularly for those who value their online privacy. This article will guide you through the concept of the darknet, its components, and how the abacus darknet url fits into the broader picture of online anonymity and safety.
We understand the importance of trust in the digital age, which is why we have implemented robust security measures to safeguard your personal and financial information. We do not operate Abacus Market or any darknet service. Follow all security recommendations in the Darknet Bible and never reveal personal information. All vendors undergo PGP verification and manual review.
What is the Darknet?
The darknet is a part of the internet that is not indexed by traditional search engines. It is accessed via specialized software, allowing users to operate anonymously. The darknet is often associated with illegal activities; however, it also serves legitimate purposes, such as privacy protection and free speech in oppressive regimes.
Characteristics of the Darknet:
- Anonymity: Users can browse and communicate without revealing their identities.
- Specialized Software: Access requires tools like Tor (The Onion Router) or I2P (Invisible Internet Project).
- Content Variety: Ranges from legal content (forums, activism) to illegal markets and services.
Understanding the Abacus Darknet URL
- We can see this pattern on the chart below, which shows the level of market share controlled by the dominant market of each epoch.
- The abacus market, once confined to physical storefronts, has evolved into a dynamic online marketplace.
- These defensive governance, risk management and compliance services not only maximize your security, but ensure your organization maintains regulatory compliance with institutions such as the SEC and FCA.
- The ordering process is simple and will be familiar to anyone who has used darknet markets before.
- Darknet markets still made $2 billion in 2024 even with increased law enforcement pressure.
The abacus darknet url specifically refers to a unique address or resource found within the darknet ecosystem. It is typically used to access platforms that focus on security, privacy, and data protection tools. Here are some key aspects to consider:
Features of Abacus Darknet URL:
- Privacy-Centric: Designed for users seeking refuge from surveillance and data tracking.
- User-Friendly: Often includes guides and resources to help navigate the darknet safely.
- Community Support: Provides forums for users to discuss experiences and seek assistance.
How to Access the Abacus Darknet URL
Accessing the abacus darknet url requires the use of specific software. Follow these steps to visit the url safely:
- Download Tor Browser: This is the most common method to access the darknet.
- Connect to the Internet: Ensure your connection is stable and secure.
- Launch Tor: Open the Tor browser once it’s installed.
- Input the URL: Enter the abacus darknet url to navigate to the site.
FAQs
1. Is using the darknet illegal?
No, using the darknet itself is not illegal. However, engaging in illegal activities, such as purchasing illicit goods or services, is against the law.
2. How can I protect my identity while using the darknet?
Use a VPN in addition to the Tor browser, avoid sharing personal information, and consider using secure email services.
3. What types of services can I find on the darknet?
The darknet hosts a variety of services, including forums, marketplaces, privacy tools, and activist platforms.
Conclusion
The abacus darknet url serves as a portal into a world focused on privacy and security. Whether you are looking for information or are simply curious about the darknet, understanding how to safely navigate this space is essential. Always prioritize your privacy and security as you explore these online resources.