Upon discovering clues of illegal activities, they should promptly report to relevant departments and provide technical support and assistance for related investigations and inquiries. Local governments at all levels give full play to the role of local monitoring and early warning mechanisms. Overseas entities and individuals are not allowed to provide virtual currency-related services to domestic entities in any form. They do not have legal tender status, should not and cannot be circulated and used as currency in the market.
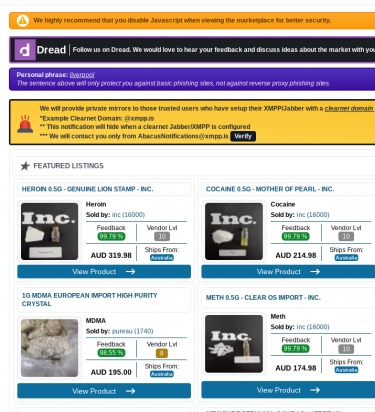
Abacus darkweb was founded in 2015 with the mission to provide a secure and reliable platform for individuals and organizations to access the Abacus site darknet network. It is one of the most active and up to date markets and always provides new and updated malware and data. Established in 2022, WizardShop is one of the biggest data stores on the dark web, focusing mainly on carding and financial data. Torzon Market has established itself as a significant player in the darknet ecosystem, offering a secure, user-centric platform for anonymous trading. Established in 2022, Torzon market is one of the biggest and most diverse marketplaces on the dark web. Established in 2019, Russian Market is a well-known and highly regarded data store on the dark web, specializing in the sale of PII and various forms of stolen data.
The concept of the darknet evokes a sense of mystery and intrigue, wrapped in layers of anonymity and complex networks. Among these, abacus darknet has emerged as a notable reference, representing an intersection of technology and privacy. As society becomes increasingly entwined with the digital realm, understanding the mechanics of the darknet, particularly the abacus darknet, is crucial for both awareness and safety. In this article, we delve into what abacus darknet entails, its significance, and the implications for users navigating this enigmatic part of the web.
Businesses conduct dark web exposure assessments to see if their customer data or credentials are circulating for sale. Stolen data sold on a darknet site today can fuel tomorrow’s account takeover breaches and ransomware attacks impacting both individuals and businesses. This sustained activity matters because these markets are hotbeds of cybercrime.
What is the Darknet?
The darknet is a part of the internet that is not indexed by traditional search engines. Accessing it typically requires specific software, configurations, or authorization. The most well-known darknet network is Tor, which utilizes a system of layered encryption to allow users to remain anonymous. This has made the darknet a haven for those seeking privacy for various reasons—be it for political activism, illicit trade, or personal security. However, not all activities in the darknet are illegal, making it a space of both risks and opportunities.
Understanding the Abacus Darknet
Abacus darknet refers to a specific implementation of darknet technologies designed to enhance computational tasks while maintaining user anonymity. This network aims to facilitate secure transactions and communication, employing an 'abacus' approach to data processing. This duality of purpose—combining anonymity with a focus on computational efficiency—sets the abacus darknet apart from other darknet iterations.
The Technology Behind Abacus Darknet
The technological structure of abacus darknet integrates advanced algorithms, cryptographic protocols, and peer-to-peer networking. By utilizing these technologies, the network efficiently processes data while ensuring that user identities and transactions remain obscured. Users engaging with the abacus darknet rely on encryption methods that provide not just anonymity, but also a safeguard against potential data breaches.
Legitimate Uses of Abacus Darknet
While the abacus darknet might be associated with questionable activities, it is essential to highlight its legitimate applications. Many individuals and organizations utilize the darknet for various purposes, including:

- Political Activism: In regions with heavy censorship, activists can use abacus darknet to share information without fear of government retribution.
- Whistleblowing: Whistleblowers can report corruption or malpractice securely through the features offered by the abacus darknet.
- Privacy-Conscious Communication: Individuals concerned about surveillance can communicate safely without compromising their identities.
Risks Associated with Abacus Darknet
Despite its potential benefits, the abacus darknet is not without risks. The same anonymity that protects users can also embolden malicious actors. Users are susceptible to:
- Fraud and Scams: The lack of regulation means that many users may encounter fraudulent activities.
- Malware Threats: Downloading from unknown sources can expose users to harmful software.
- Legal Consequences: Engaging in illegal activities, even on the darknet, can lead to serious legal ramifications.
Navigating the Abacus Darknet Safely
For those who choose to explore the abacus darknet, taking precautions is essential. Here are some best practices:
- Use a VPN to add an extra layer of anonymity.
- Engage only with trusted sources and communities.
- Be wary of sharing personal information.
- Keep software up to date to protect against vulnerabilities.
- A single log might contain dozens of credentials across multiple services.
- Users started reporting withdrawal issues and delays, prompting concern on darknet forums.
- Darknet markets still made $2 billion in 2024 even with increased law enforcement pressure.
- Russian Market and 2easy focus almost exclusively on stealer logs and credentials.
Conclusion
The abacus darknet embodies the complexity of our digital age—a space where anonymity meets necessity. As users become more informed about the functioning and implications of the darknet, they can make safer choices when navigating this hidden part of the internet. Understanding the abacus darknet not only helps demystify its operations but also speaks to the broader themes of privacy, security, and digital ethics in our technology-driven lives.