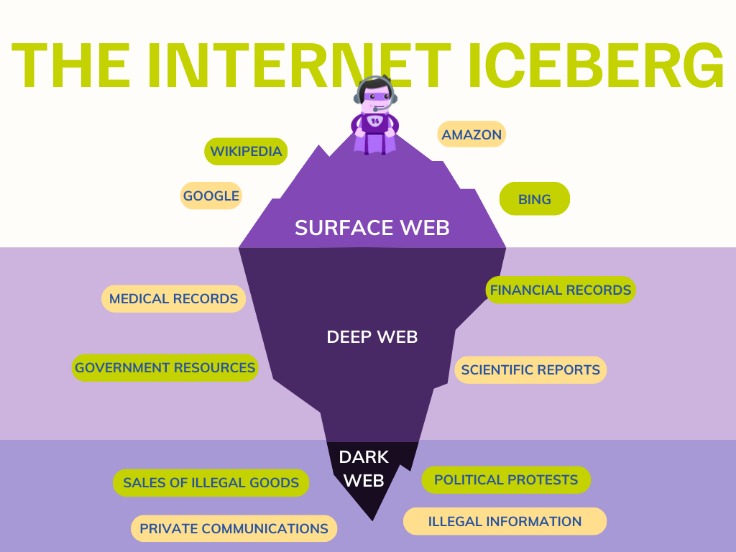
The .onion dark web is a hidden part of the internet that often captures the imagination due to its association with anonymity and illicit activities. However, it is essential to understand both the opportunities and risks associated with this obscure online realm. In this article, we will explore what the .onion dark web is, how it works, its legitimate uses, and important safety considerations for those who might venture into it.
Lastly, much of the content on the dark web is not traditionally accessed making it likely that your organization could have that content blocked limiting your research results. If dark web access is approved, the speed, security and anonymity of that access depends on the way access is delivered. While anyone can download Tor to access the dark web, professionals conducting sensitive online research should access and use it in line with their organization’s policies. Tor (The Onion Router) is a free network designed to provide online anonymity and privacy. Engaging in criminal activity, accessing illegal content, or participating in unlawful transactions is a criminal offense. Their crawlers do not index .onion domains or any content on the Tor network.
.onion Dark Web
You might notice that our hidden service does experimentally listen to HTTPS connections, but we’re currently using a self-signed key for that, which can cause a combination of browser errors and assets not loading if you try to visit our onion site that way. The 16 characters of the hostname before .onion are actually derived from this key, which allows Tor to confirm that it is connected to the right hidden service. A Tor hidden service (sometimes called an “onion site” or an “onion service”) has a special domain name that ends in .onion – like p53lf57qovyuvwsc6xnrppyply3vtqm7l6pcobkmyqsiofyeznfu5uqd.onion – that you can only connect to using Tor. While using our Tor hidden service greatly increases your privacy, it’s important to note that it is, for the most part, the same website people see on the regular Internet. Some users connect to a VPN before accessing Tor to protect against ISP monitoring, although this may slow down connection speeds.
The .onion dark web refers to websites that are accessible only through the Tor browser, which anonymizes users by routing their internet traffic through a series of servers. This process makes it challenging to trace the users' identities and locations. While often portrayed negatively, the .onion dark web hosts a variety of content beyond illegal activities.
- Using these search engines responsibly allows us to gather that intelligence quickly and safely, without stumbling into illegal territory.
- Addresses tend to be a mix of random numbers and letters, making them challenging to remember or access manually.
- For investigations, safe access and governance matter more than volume.
- The second category consists of data stores, which specialize in stolen information.
How the .onion Dark Web Works
The ability to access only known contacts provides a higher degree of trust than other software. Another network is I2P, or the “Invisible Internet Project,” released in 2003. By distributing the information through many hosts, it makes it nearly impossible to track down or scrub all of the pieces of content from the web. The content is made available via BitTorrent, which shares bits of information across many peers, each one hosting a piece of the information needed.
- Donations from organizations like Mozilla and Electronic Frontier Foundation help fund the development of privacy tools and keep Tor accessible.
- Curious about what’s lurking in the shadows of the internet?
- But I will never know because it’s gone now.
- So with all this illegal activity taking place on to the dark web, is it really okay to log on?
- If you’ve never browsed the dark web before, you probably weren’t expecting to see several websites with About Us pages.
To access the .onion dark web, users must install the Tor browser, which is specifically designed to handle .onion domains. Here’s a brief overview of how it operates:
- Anonymity: When users connect to a website on the .onion dark web, their data is encrypted and sent through multiple relays, ensuring their privacy.
- Special Domains: Websites on the .onion dark web have unique .onion addresses instead of traditional .com, .org, or .net.
- Access Restrictions: Many standard browsers cannot access these sites, reinforcing their exclusivity.
Legitimate Uses of the .onion Dark Web
While the .onion dark web is often linked with illegal activities, it also serves legitimate purposes, such as:
- Privacy Protection: Individuals in repressive regimes may use the .onion dark web to communicate and share information without fear of persecution.
- Whistleblowing Platforms: Sites like SecureDrop allow whistleblowers to submit information securely and anonymously.
- Research and Education: Journalists and researchers utilize the .onion dark web for investigating sensitive topics without exposing their identities.
Safety Considerations
While exploring the .onion dark web can be intriguing, users must exercise caution to protect themselves:
- Use a VPN: Combining Tor with a reliable VPN adds an extra layer of security to your browsing.
- Avoid Sharing Personal Information: Anonymous browsing does not guarantee safety; refrain from providing identifiable information.
- Verify Sources: Be cautious of scams; not all sites on the .onion dark web are trustworthy.
FAQs about the .onion Dark Web
Q: Is everything on the .onion dark web illegal?
A: No, while illicit activities are present, many legitimate sites exist that promote privacy and freedom of expression.
Q: Do I need special skills to use the .onion dark web?
A: No, using the Tor browser is straightforward, and many resources guide new users on navigating the space safely.
Q: Can I get in trouble for visiting .onion dark web sites?
A: Simply visiting a .onion site is not illegal, but engaging in illegal activities can result in legal consequences.
Understanding the .onion dark web is crucial, especially in our digital age, where privacy and security are paramount. Whether for legitimate reasons or alternative exploration, awareness and caution can ensure a safer experience online.