The internet is a vast landscape filled with information, communities, and services, but not all of it is accessible through standard search engines. One intriguing facet of the web is the dark web, a section often misunderstood and shrouded in mystery. Understanding how to access the dark web is essential for those interested in exploring its opportunities and risks, especially as it pertains to online privacy and security. This article aims to shed light on the dark web, its purposes, and important safety considerations.
Understanding the differences between the deep web vs dark web is crucial for the safe and responsible use of the internet. To understand the differences in the dark vs deep web, one comes to realize that there are legitimate uses and significant risks in both layers. Unlike the deep web vs dark web that encompass such secrecy or illegality, this surface web is totally safe to be used daily as well as it falls under more familiar laws and regulations. Unlike the surface web, which is easily accessible and often serves legitimate purposes, the deep web holds valuable information that typically requires specific access credentials or subscriptions. The deep web vs dark web are often misconstrued as being one thing when in reality they represent two different levels of the internet.
What is the Dark Web?
- Attackers constantly search for these misconfigurations, and stolen data appears on dark web markets within hours of discovery.
- Poisoned nodes—compromised nodes on a network that secretly surveil traffic—can also poke a hole in anonymity.
- Many people use the dark web to access information freely, without fear of tracking or censorship, and to preserve their privacy.
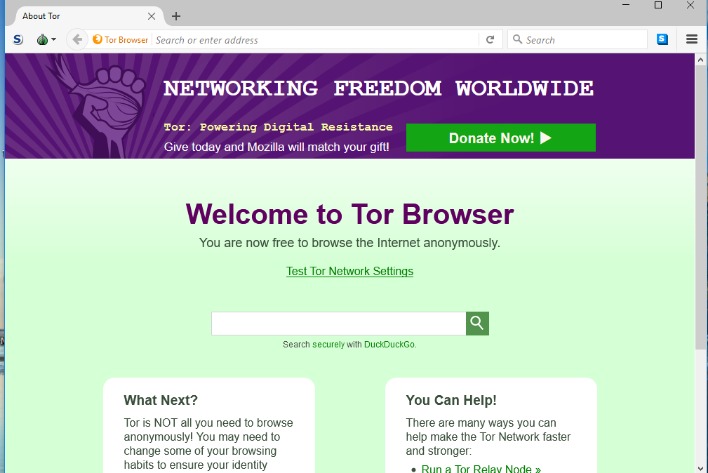
- When you use Tor, which routes your internet traffic through many different relay nodes, your online activity is obscured because you’re browsing anonymously.
The dark web refers to a portion of the internet that requires specific software to access, making it distinct from the surface web, which most users encounter daily. Often characterized by anonymity and privacy, the dark web hosts various platforms, forums, and marketplaces that can be both beneficial and harmful.
How to Access the Dark Web
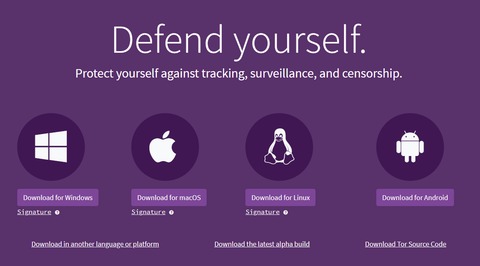
To access the dark web, users typically utilize special software such as Tor (The Onion Router). Tor anonymizes user activity by routing internet traffic through a network of volunteer nodes, protecting the user's identity and location. Here’s a step-by-step guide to accessing the dark web safely:
- Download Tor Browser: Obtain the Tor Browser from the official website to ensure you have a legitimate version.
- Install the Browser: Follow the installation instructions to set up the browser on your device.
- Connect to the Tor Network: Open the Tor Browser and click on "Connect" to start using the network.
- Navigate to .onion Sites: Use specific web addresses that end in .onion to access dark web content.
Why People Access the Dark Web
Individuals may seek to access the dark web for various reasons, including:
- Privacy Protection: Many users are concerned about surveillance and want to communicate or share information without being tracked.
- Whistleblowing: The dark web provides a platform for those wishing to expose wrongdoing without fearing retaliation.
- Access to Censorship-Free Information: In regions with heavy censorship, the dark web can offer a means to access uncensored news and information.
Risks and Safety Precautions
While the dark web has its benefits, it is essential to acknowledge the risks involved. Users face potential threats, including:
- Scams and Fraud: Many dark web sites may not be trustworthy, leading to financial loss or personal data theft.
- Legal Consequences: Accessing certain content or engaging in illegal activities on the dark web can result in severe legal repercussions.
- Exposure to Harmful Content: Users may inadvertently come across disturbing or illegal materials.
To navigate these challenges safely, consider the following precautions:
- Use a VPN: A Virtual Private Network can offer additional protection for your data and enhance anonymity.
- Be Cautious with Personal Information: Never share identifiable information when interacting with others on the dark web.
- Avoid Downloading Files: Unverified downloads can carry malware that compromises your device's security.
Conclusion
The ability to access the dark web opens a world of opportunities for those seeking privacy and uncensored information. However, it is critical to approach with caution and awareness of the risks involved. By understanding the intricacies of the dark web and taking the necessary safety measures, users can explore this hidden side of the internet responsibly.